David Kountz
Information Security | CompTIA Security+ | SOC & GRC
BS Information Systems | CompTIA Security+ | Aspiring Security Engineer
I'm an Information Security professional based in Jacksonville, FL, with a BS in Information Systems from the University of North Florida (GPA: 3.8) and a CompTIA Security+ certification. My background spans both GRC and hands-on technical security work, and I'm actively transitioning into a security engineering or SOC analyst role.
At CSX, I worked on the Information Security GRC team where I built Python automation tooling for SOX compliance workflows, integrated with tools like Selenium, Pandas, and ldap3, and contributed to AI agent evaluation for compliance use cases. That experience gave me a strong foundation in enterprise security operations, IAM, and audit processes.
Outside of work, I've built and operate a multi-VM SOC home lab using Wazuh, Sysmon, and Kali Linux. I simulate real attack scenarios — SSH and RDP brute force, credential attacks — investigate the resulting alerts, and produce formal incident reports mapped to MITRE ATT&CK. This hands-on practice keeps my detection and investigation skills sharp.
I'm currently pursuing CySA+ and continuously expanding my knowledge in threat detection, incident response, and security tooling. I'm excited to bring both my automation background and security fundamentals into a role where I can make a real impact.
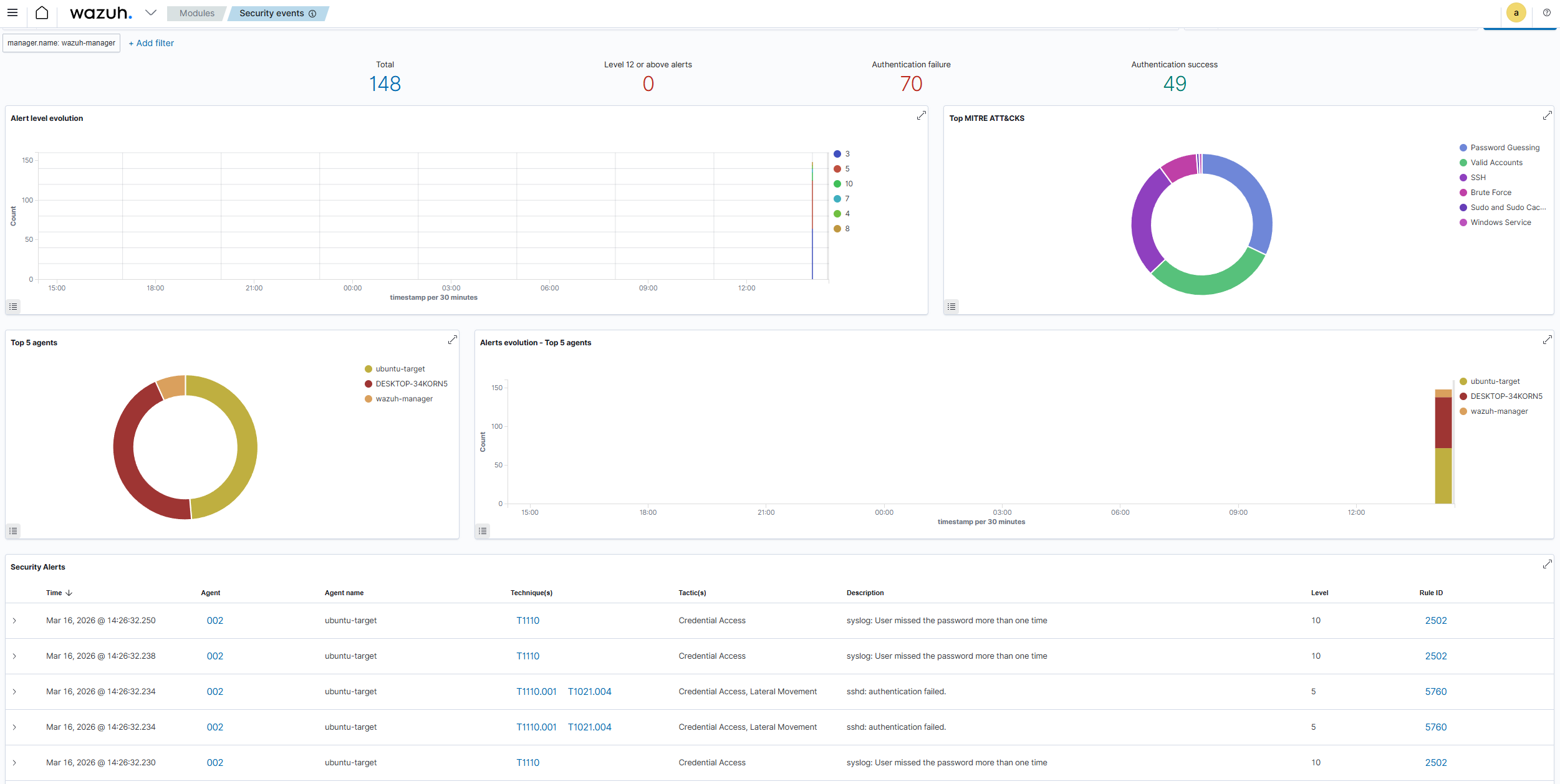
A multi-VM isolated SOC environment using Wazuh, Sysmon, and Kali Linux for threat detection and incident investigation.
A cybersecurity blog made using Node.js, React, and utilizing a PostgreSQL database for the back end.
The site you are currently on.

A full-stack weather dashboard with real-time data and 5-day forecasts.
A fully isolated, multi-VM Security Operations Center lab environment built to simulate real-world attack scenarios, practice alert investigation, and produce formal incident reports mapped to MITRE ATT&CK.
Tech Stack: Wazuh 4.7.2, Sysmon (SwiftOnSecurity ruleset), auditd, Hydra, Nmap, VirtualBox, Kali Linux, Ubuntu 22.04, Windows 11, PowerShell
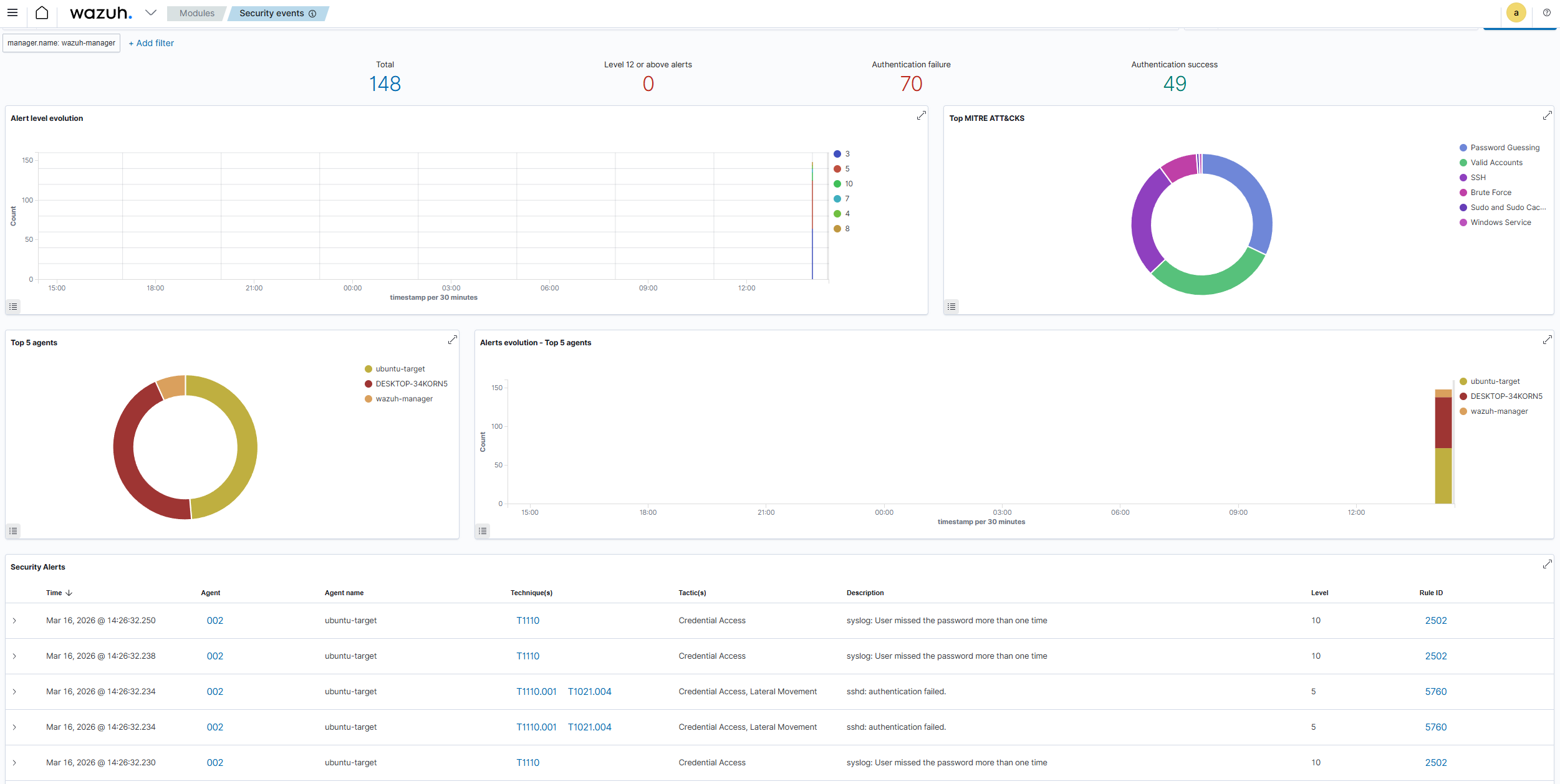
Lab network diagram: Wazuh Manager (10.0.2.10), Windows 11 Target (10.0.2.20), Ubuntu Target (10.0.2.30), and Kali Attacker (10.0.2.50) on an isolated VirtualBox NAT network.
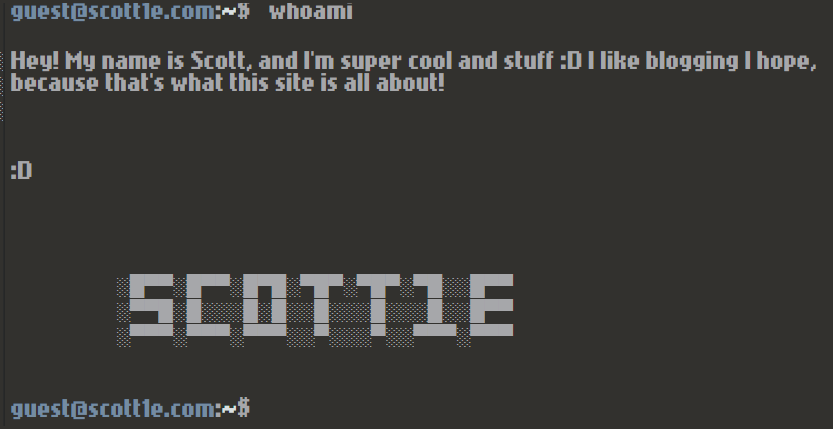
A cybersecurity blog site that features a fully workable faux Linux terminal for its UI.
Tech Stack: Node.js, React, PostgreSQL. Utilizing AWS EC2 instance for hosting and RDS for the PostgreSQL database.
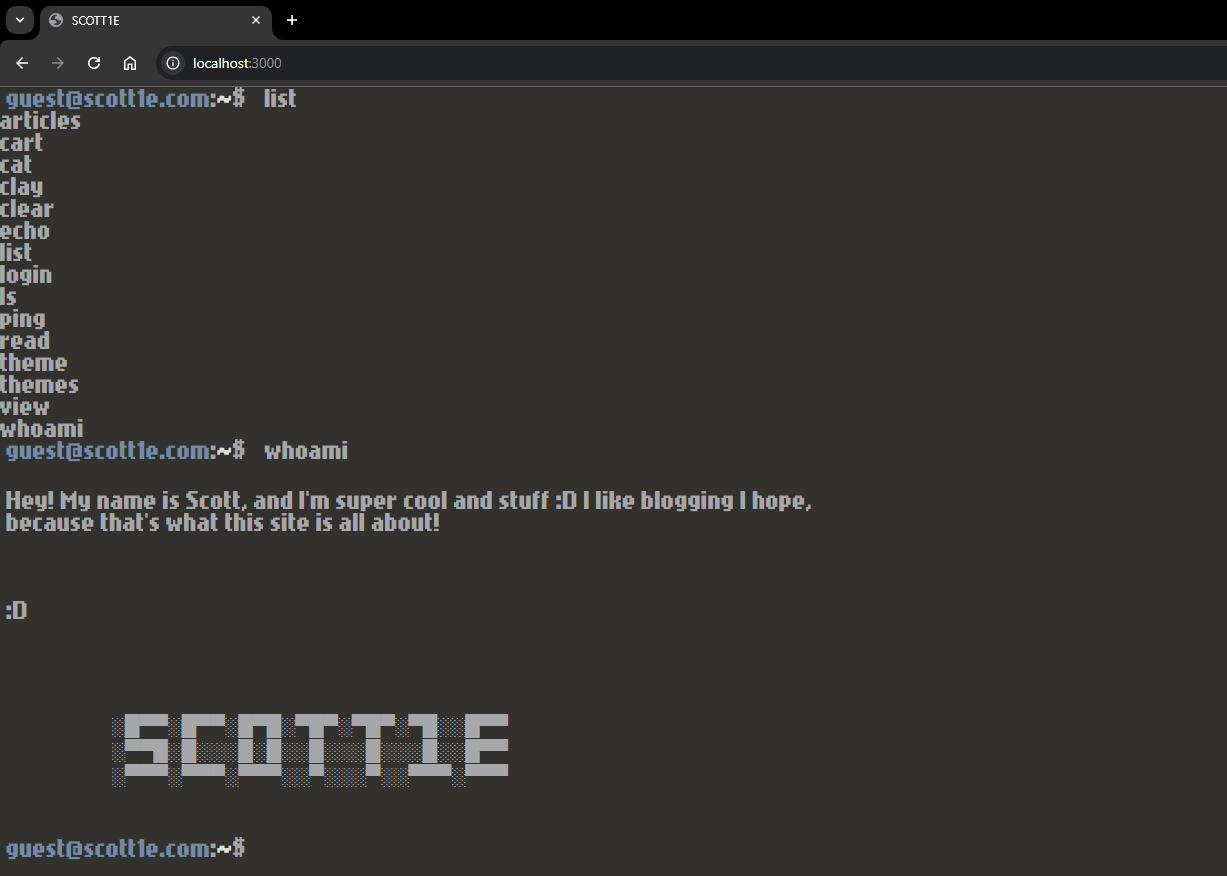
Faux Linux terminal interface with 10+ commands for article navigation, theme swapping, and information on site author, Scotty.
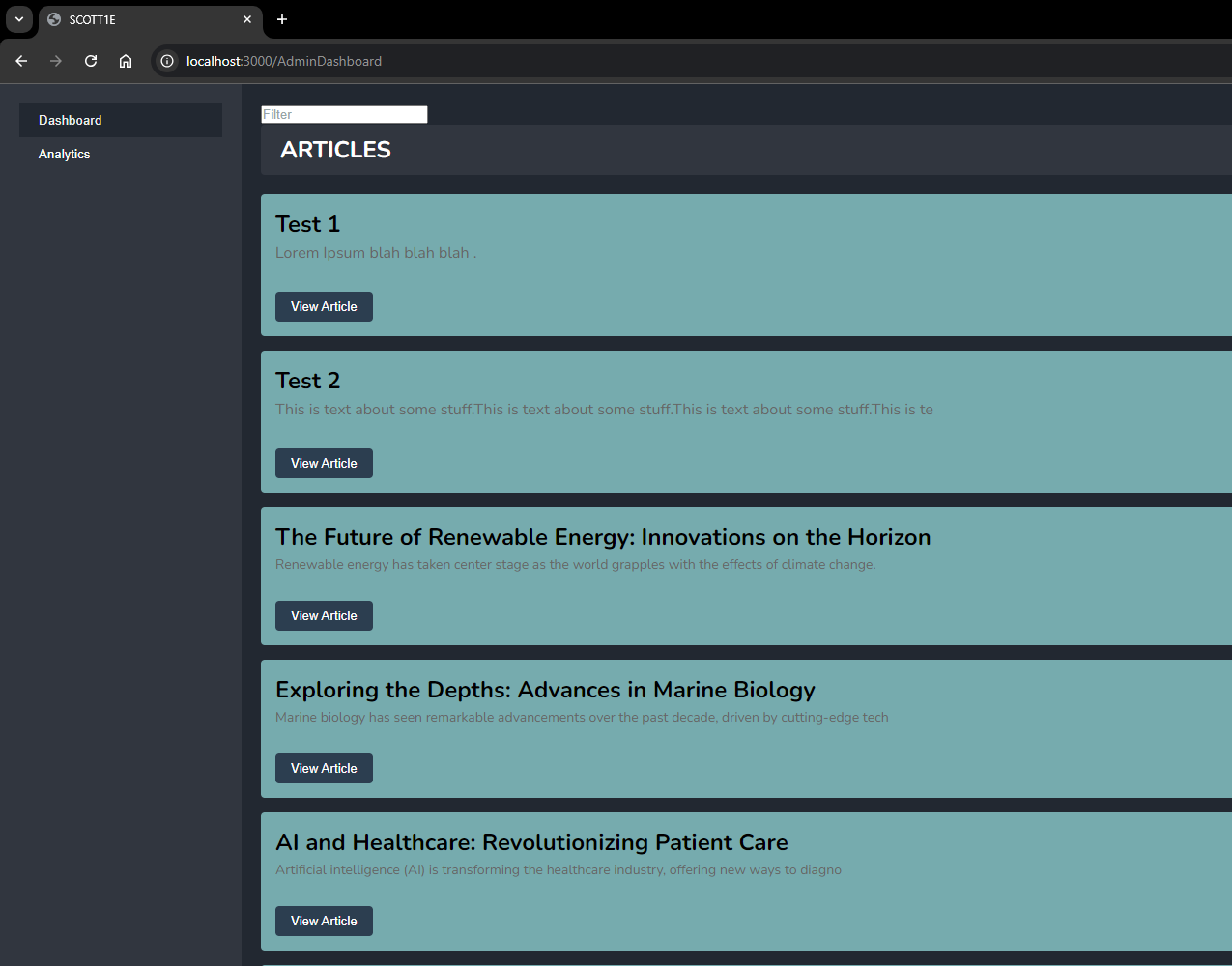
Admin dashboard for site maintenance, article management, and analytics. Prioritizing security, utilizing data encryption, access control, and database security practices to ensure that sensitive data is protected and secure.
This project consisted of a team of 4 individuals and was part of the Senior Project capstone course for my degree at UNF.
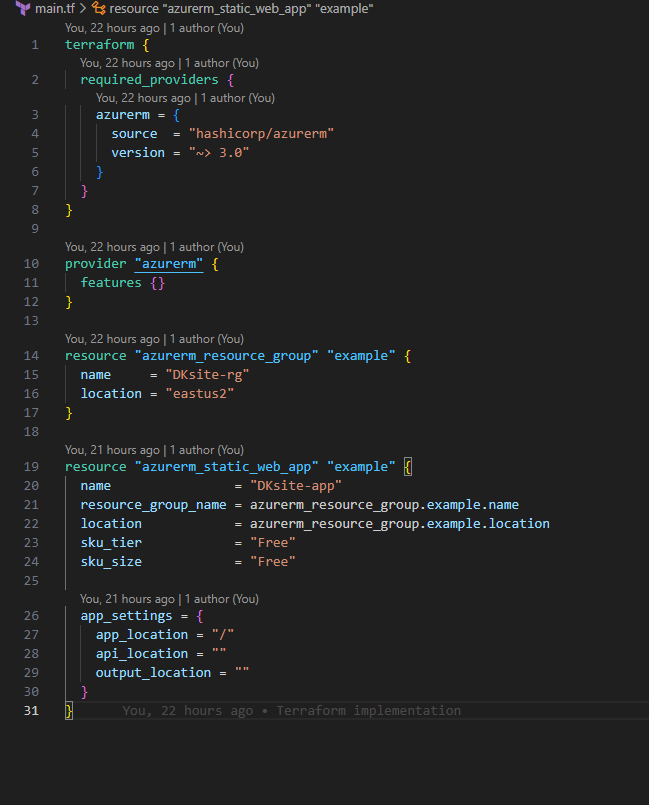
The website you are currently on.
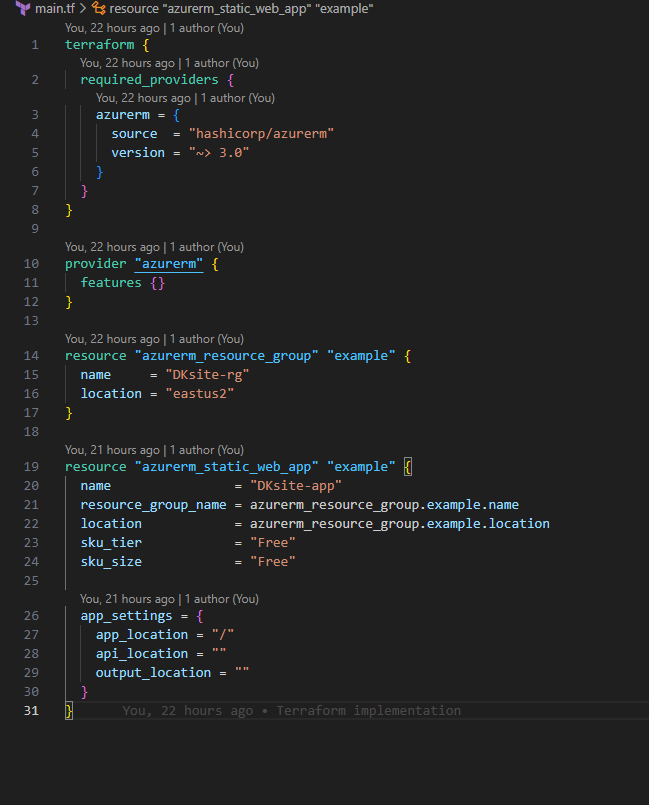
Utilizes Terraform as a CI/CD pipeline for automated updates to the Azure Web App.
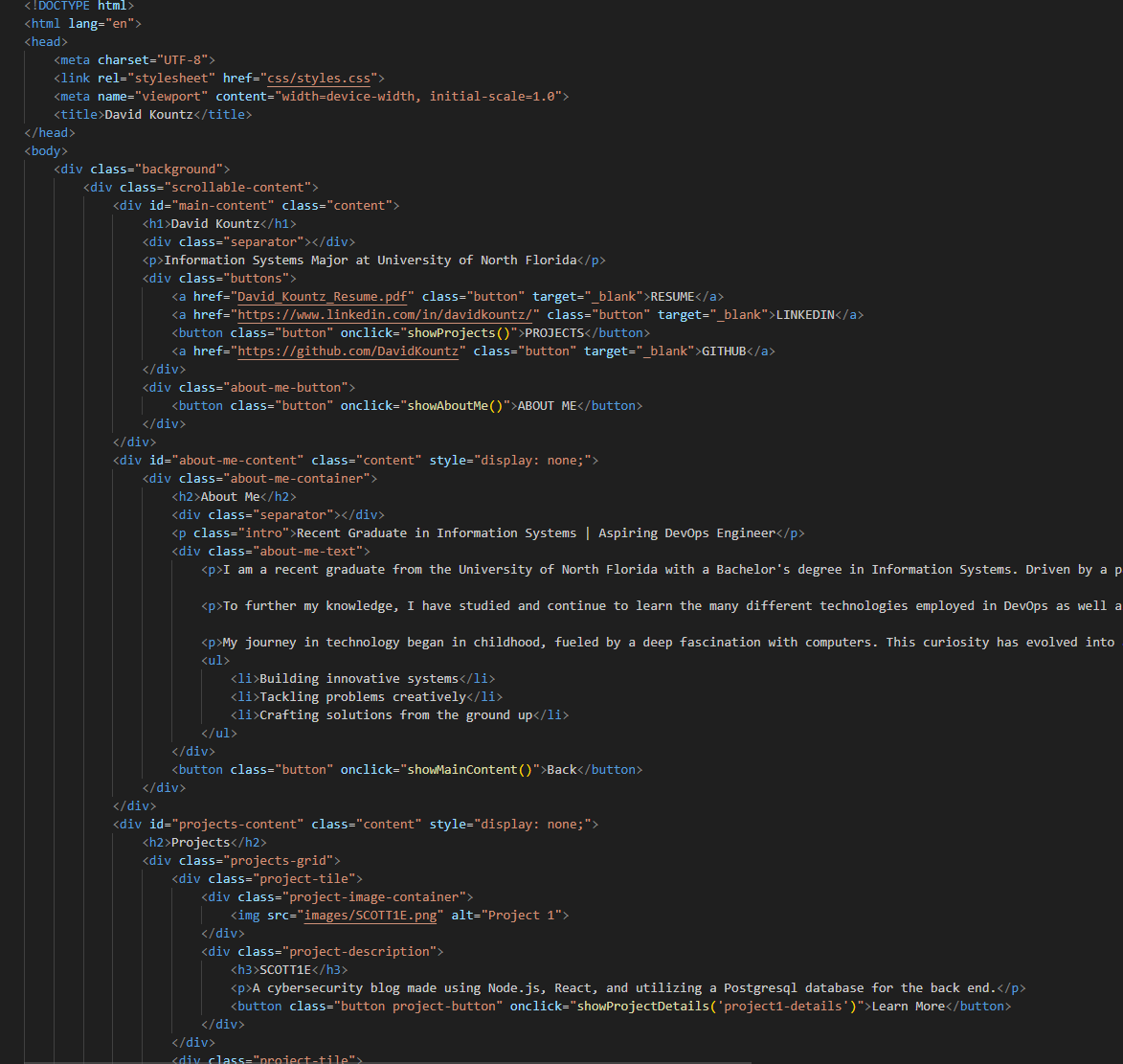
GitLab repository for added automation integration.
A full-stack weather application providing real-time weather data and forecasts with an intuitive user interface.
Tech Stack: React, Spring Boot, OpenWeatherMap API, Java, JavaScript, Responsive Design

The main dashboard displays current weather conditions, temperature, humidity, wind speed, and sunrise/sunset times for the searched location.
This project started as a way to practice frontend-backend integration while creating something practical that users would find valuable. I designed the application to be intuitive, with a clean interface that prioritizes the most important weather information.
The biggest challenge was optimizing API usage to stay within rate limits while ensuring users always have access to current data. I implemented a backend caching system that stores weather data for 30 minutes, significantly reducing API calls while maintaining data freshness.